You’re probably familiar with the phrase, “Don’t reinvent the wheel.” The wheel is a very old and very simple concept, but there’s a reason it has withstood the test of time and remains unsurpassed. In a nutshell, it works remarkably well for its intended purpose. When it comes to hacking, this is true for SQL injection (or SQLi). It is a very old and very simple attack, but it remains one of the most effective, which is why it plays such a significant role in the latest Alert Logic Cloud Security Report.
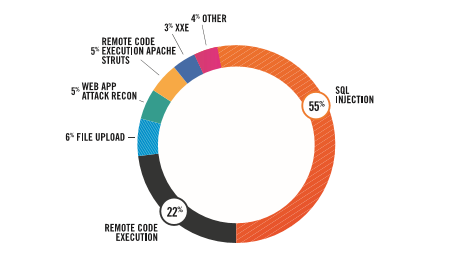
Four-fifths of all web application attacks we detected during the 18-month period analyzed for the Cloud Security Report can be attributed to two popular methods: SQL injection and remote code execution. SQLi alone was behind 55 percent of all observed attacks.
Developers and cyber security professionals have known about the concept and risks of SQLi for nearly 20 years, and yet it remains one of the most prevalent and effective cyber threats. One website that monitors and catalogs SQLi events lists 75 major cyber attacks resulting from SQLi just since the beginning of 2016. The US Election Commission, Epic Games, Facebook, Instagram, and even McAfee – which is in the business of cyber security – were caught with their SQL injection pants down. Major incidents like the 2009 data breach of Heartland Payment Systems were also the result of SQLi.
Although SQLi isn’t new, and it ranks as a relatively simple cyber attack technique, we also identified a concerning trend in the Cloud Security Report. In most of the instances that resulted in a data breach, SQLi played a crucial role and was employed with a high degree of complexity and sophistication. The Cloud Security Report explains, “8-10 percent of the customers we monitored were targeted by actors with better-than-average levels of skill and determination, which is notable. These actors used various forms of obfuscation and personally created sophisticated SQL injection attacks more complex than common tooling – such as SQLMap, Burp Collaborator Suite or Havij – support.”
It’s also important to note that SQLi attacks are often noisy and hard to separate from legitimate activity. Identifying SQLi attacks relying solely on humans for analysis is challenging. Alert Logic addresses that challenge by applying machine learning as well.
A combination of expert cyber security analysts in the Alert Logic security operations center (SOC) and machine learning enabled us to identify the root cause of cyber attacks and identify incidents where SQLi was successful. More than 44 percent of the successful SQLi attacks we identified resulted in disclosure of information about the database itself – things like the type and version of the database, or information about the structure of the database. Nearly 40 percent of the successful SQLi attacks allowed the attacker to identify tables or field names and other details about the database. Just over 17 percent of successful SQLi attacks resulted in an actual data breach – the compromise and exfiltration of data.
Not all SQLi attacks are successful. However, SQLi attacks still work far more often than they should and result in unauthorized access to or theft of sensitive data. Zero-day vulnerabilities make sexier headlines, but the analysis in the Alert Logic Cloud Security Report illustrates that attackers like to stick with what works – especially what works for compromising applications in public clouds. You need to consider your existing cloud security plans and take steps to be able to identify and guard against SQL injection attacks.