In today’s rapidly evolving cybersecurity landscape, protecting sensitive information is paramount, especially for businesses handling payment card transactions. The Payment Card Industry Data Security Standard (PCI DSS) is a set of security standards designed to ensure the protection of cardholder data. Within this framework, the role of a PCI Approved Scanning Vendor (ASV) plays a crucial part in fortifying an organization’s security posture. But what is a PCI ASV and who needs these scans?
What is a PCI ASV?
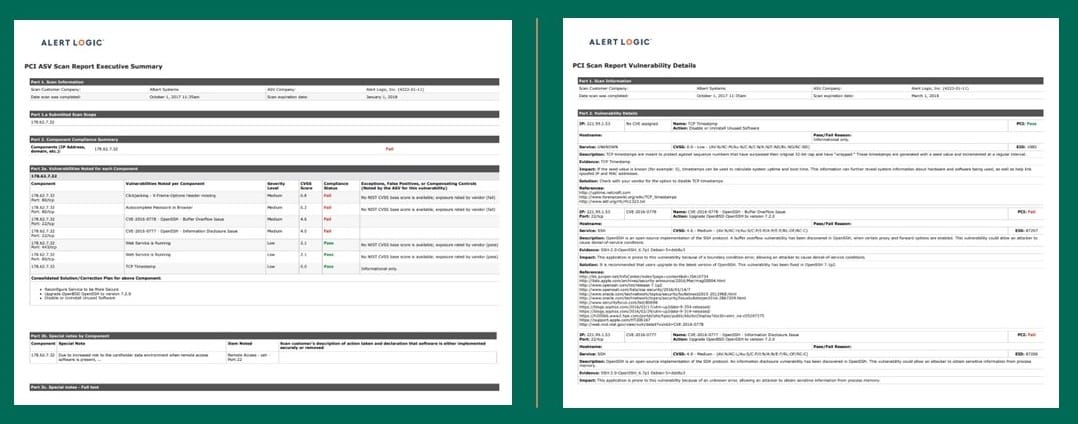
PCI DSS requires organizations to conduct regular vulnerability scans on their networks, systems, and applications. ASVs play a pivotal role in this process. An ASV is an organization approved by the PCI Security Standards Council (PCI SSC) to conduct external vulnerability scans in adherence for PCI DSS compliance requirements.
What is an ASV Scan?
ASV scans are external vulnerability scans performed by PCI SSC-approved vendors as part of an organization’s efforts to evaluate and confirm the security of systems and networks dealing with payment card data. The scans’ primary purpose is to aid organizations in upholding a secure payment card environment and safeguarding against cyber threats. ASV scans seek out vulnerabilities susceptible to exploitation by threat actors.
For PCI DSS 4.0, ASV scans validate adherence to the external scanning requirements in Requirement 11.3.2 and are a crucial element in maintaining a secure environment and ensuring compliance with PCI DSS. Qualified individuals must perform scans, ensuring clear organizational separation between testers and systems under examination.
ASV scan components and testing procedures
ASV scans involve a comprehensive examination of a network’s security architecture to identify vulnerabilities that threat actors could exploit. Per PCI SSC, the main phases of the scanning process include:
- Scoping
- Scanning
- Reporting/remediation
- Dispute
- Rescan (as needed)
- Final reporting
What if your business fails the ASV scan? You can dispute the failed scan results to your ASV; the disputing process differs among ASVs. PCI SSC does not involve itself in scan disputes.
While a failed scan can turn out to be inaccurate, for the most part, a vulnerability causes the failure. Your organization needs to take steps to fix any issue. Take note that you need to run additional scans until achieving a passing scan. You also must turn all failed scans and disputes into PCI SSC as per their requirements. If an organization fails to meet PCI DSS 4.0 requirements, not only does this increase the risk of scan failures but also may trigger potential investigations, fines, and penalties, particularly in the event of a card breach post-mandatory implementation of PCI DSS 4.0. Noncompliance repercussions can result in substantial fines, varying between $5,000 and $100,000 monthly, contingent upon the duration of non-compliance and transaction volume of the organization.
PCI DSS 4.0 Vulnerability Scanning Requirements
Why is vulnerably scanning important? Threat actors are on the lookout for unpatched or vulnerable servers to exploit for targeted assaults. An organization may miss vulnerabilities and leave itself ripe for a breach if it does not implement a regular scanning process for outward-facing devices. Because of this, PCI DSS states to conduct external vulnerability scans at a minimum of once every three months by a PCI SSC Approved Scanning Vendor.
PCI Requirement 11
PCI DSS Requirement 11 focuses on “external and internal vulnerabilities are regularly identified, prioritized, and addressed.” Regular security testing is vital because vulnerabilities are continuously found by attackers, researchers, and with new software introduction. This testing ensures security controls remain effective in an evolving environment.
Requirement 11 does focus on scanning but ASVs need to conduct internal vulnerability scans. Per the requirement, “internal vulnerability scans can be performed by qualified, internal staff that are reasonably independent of the system component(s) being scanned (for example, a network administrator should not be responsible for scanning the network), or an entity may choose to have internal vulnerability scans performed by a firm specializing in vulnerability scanning.”
The need for an ASV does come into play for PCI DSS 4.0 Requirement 11.3.2 which specifies the mandatory actions and frequency for comprehensive security scans. This requirement emphasizes the need for thorough and frequent scanning to detect any potential weaknesses promptly.
As per the requirement, perform external vulnerability scans:
- At least once every three months.
- By a PCI SSC Approved Scanning Vendor (ASV).
- Vulnerabilities are resolved and ASV Program Guide requirements for a passing scan are met.
- Rescans are performed as needed to confirm that vulnerabilities are resolved per the ASV Program Guide requirements for a passing scan.
For those organizations using the defined approach, Requirement 11 testing procedures include:
- 3.2.a Examine ASV scan reports from the last 12 months to verify that external vulnerability scans occurred at least once every three months in the most recent 12-month period.
- 3.2.b Examine the ASV scan report from each scan and rescan run in the last 12 months to verify that vulnerabilities are resolved and the ASV Program Guide requirements for a passing scan are met.
- 3.2.c Examine the ASV scan reports to verify that the scans were completed by a PCI SSC Approved Scanning Vendor (ASV).
How Can I Find an Approved Scanning Vendor?
Selecting a dependable ASV is vital to the success of your PCI DSS external vulnerability scanning requirements. The PCI SSC hosts a PCI ASV list on its website. Even when using an ASV from this list, verify chosen they meet the requirements and have expertise to safeguard your payment card information.
Fortra’s Alert Logic is a PCI ASV. The vulnerability scans we perform for our customers validate they are not vulnerable to the increasingly sophisticated attacks on their systems.
PCI ASV scans play a pivotal role in securing payment card data and achieving and maintaining PCI DSS 4.0 compliance. Ensure your organization aligns to Requirement 11.3.2 by collaborating with an experienced ASV.
Explore Alert Logic’s PCI Compliance SolutionsAdditional Resources:
PCI DSS 4.0 Compliance Solution Brief
Core Impact Helps Secure PCI DSS v4.0 Requirement 11
PCI DSS 4.0 Requirements – Restrict Access, Identify Users and Authenticate Access