Automated Unified Event Log Monitoring Across Your Environments
With a log file monitoring approach informed by leading practices, organizations can capture the right data, minimize storage requirements, meet compliance mandates, and trace back activity to gain a deeper understanding of what happened if an event occurred. Extensive log search and analysis capabilities can also be used to support forensic investigations and compliance responses should the need arise.
Deployment Automation
Automate deployment of lightweight collectors for Windows, Linux, and custom apps in your cloud and hybrid infrastructure
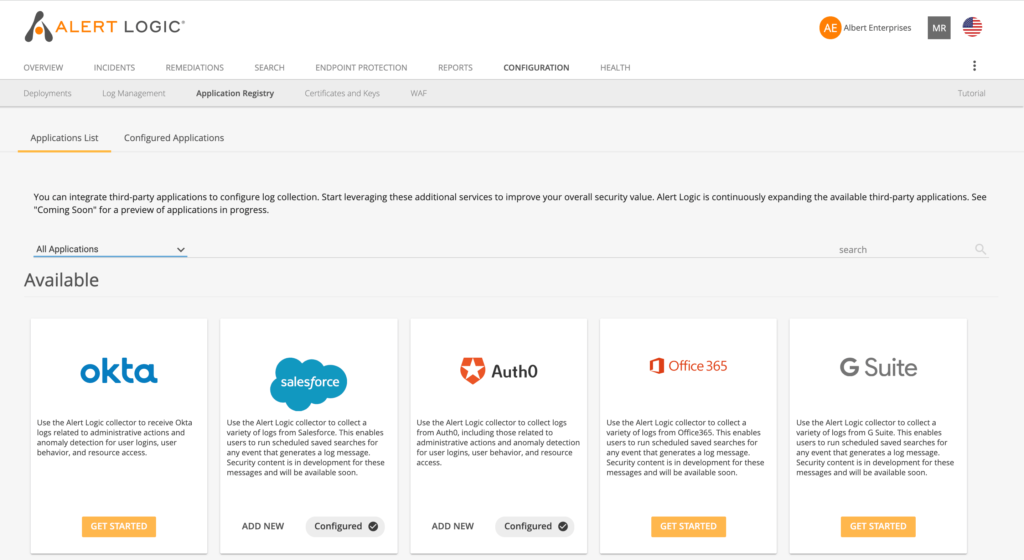
Simple Integration
Easily integrate log file data from applications, workloads, and infrastructure assets
User Activity Tracking
Track user activity and suspicious behavior in real time across all your environments
Collect & Aggregate
Collect, aggregate, and search log data from container application logs with our Container Security Solution.
Alert Logic’s automated log monitoring platform provides comprehensive visibility for your cloud, hybrid, and on-premises environments
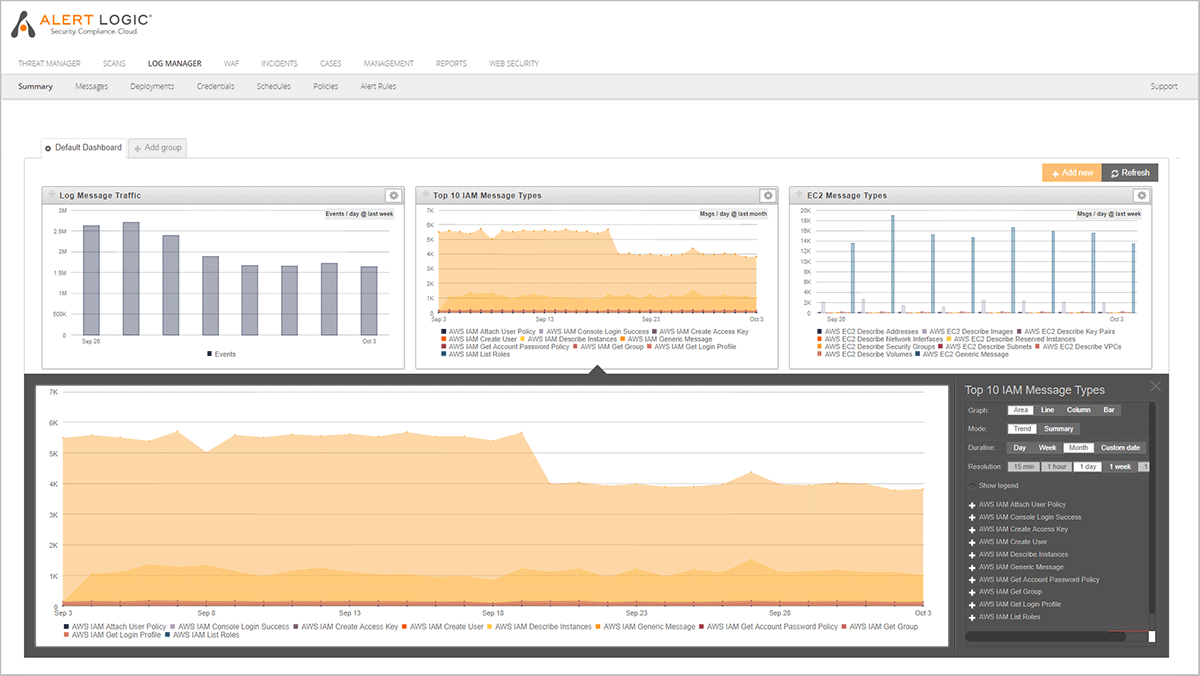
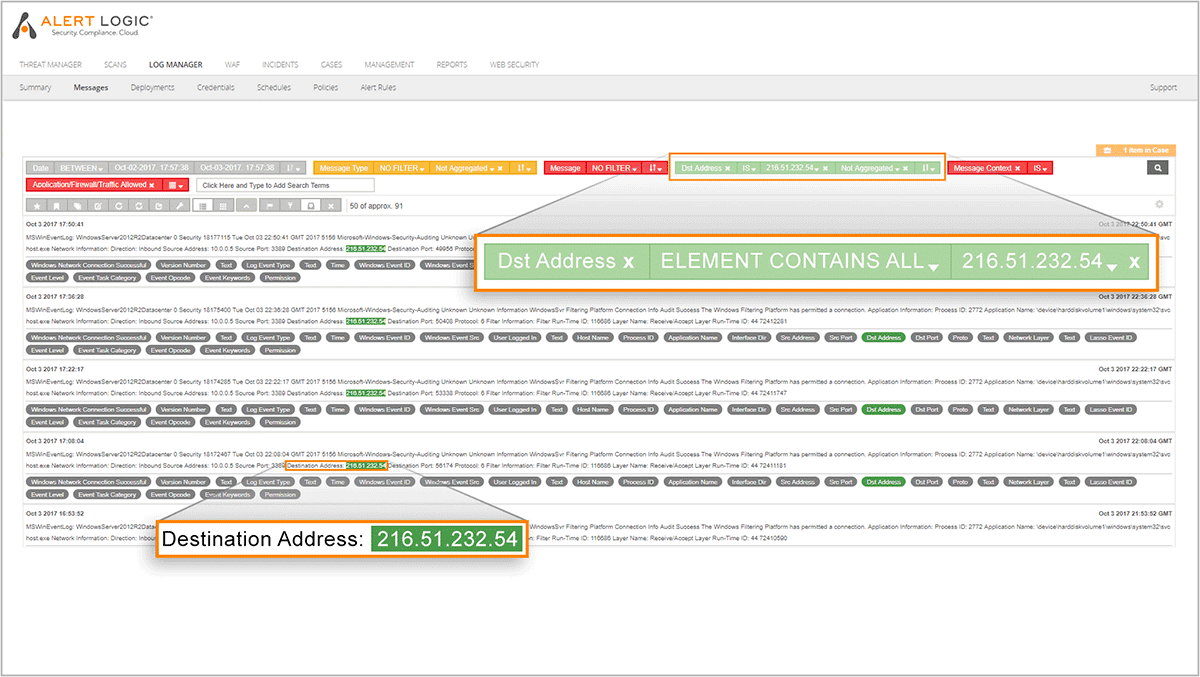
Log Analysis for Threat Detection and Forensics Answers
- Quickly identify indicators of compromise, potential breaches, or run incident response forensics.
- Focus on remediating threats quickly including unauthorized privilege escalations, brute force attempts, malicious user identity, and access activities.
- Access log data that has been processed, analyzed and correlated with 4,800+ security parsers
- Identify and research events:
- AWS—CloudTrail, S3, EC2, IAM, AWS-deployed containers
- Azure—Monitor, Storage Accounts, and AppServices, Azure-deployed containers
- Office 365—User Activity, Admin Changes, SharePoint, and ActiveDirectory services
- Available in Alert Logic Professional and Alert Logic Enterprise Managed Detection and Response offerings.
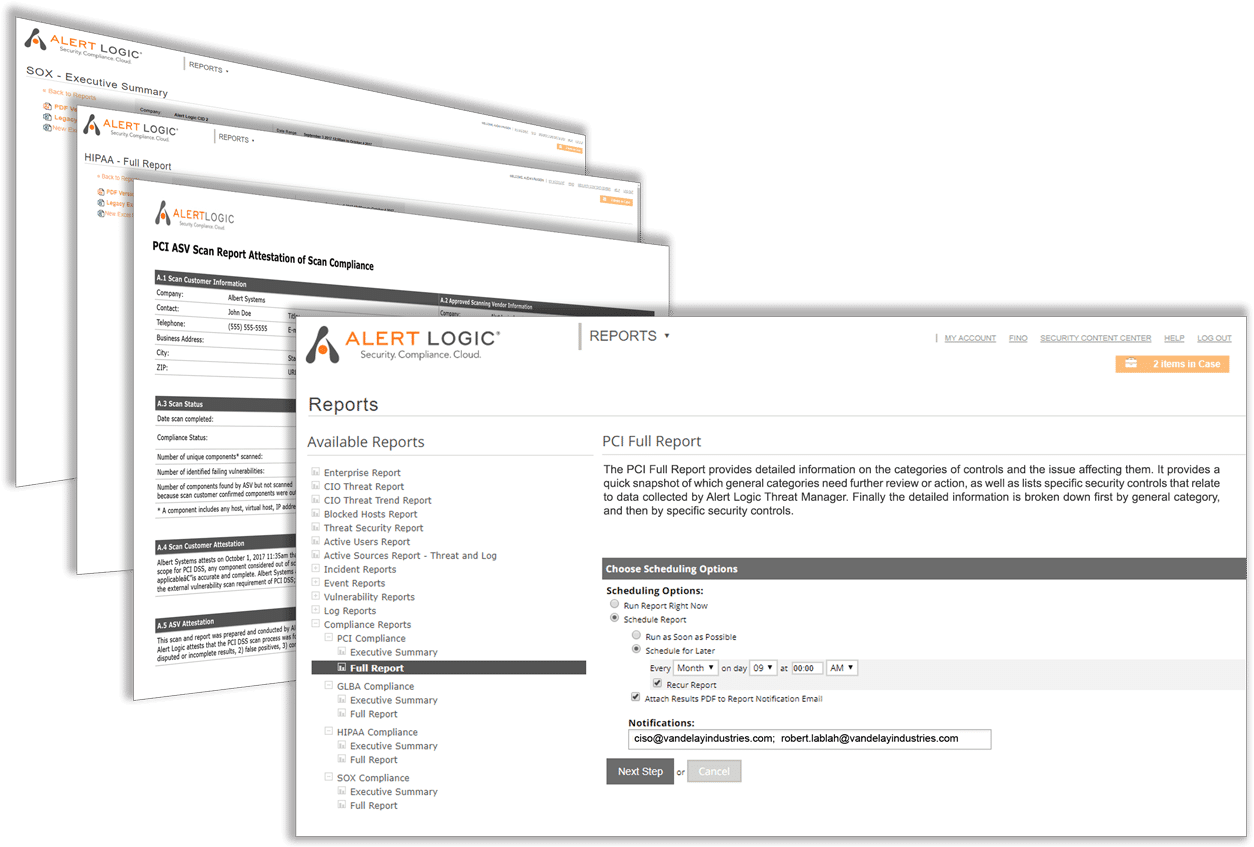
Quickly Access Years of Raw and Parsed Log Data
Centralized, cost effective log storage puts the information you need for forensics and compliance audits at your fingertips.
- Reduce costs associated with storage, maintenance and replication. Log storage options designed to meet your needs.
- Access, conduct log analysis, report, and audit raw and normalized event log data anytime
- Comply with regulations that require long-term, auditable log retention such as GDPR, PCI DSS, SOX, and HIPAA
- Count on us to store and manage petabytes of log data—protected against loss, unauthorized access or modification in our SSAE 18 verified data centers
Our Commitment to Data Security
Alert Logic maintains strict compliance with internal and external regulatory requirements for our IT operations and services, including: PCI DSS 3.2, AICPA SOC 2, Type 2, and ISO 27001-2013 certification for UK Operations.


Need to Schedule A Demo?
Please fill out the form below in its entirety or call us directly at 844.816.1051, for the UK call +44 (0) 203 011 5533.