24/7 Expert Threat Management
Powered by machine learning and advanced analytics, the platform, combined with our expertise, takes broad data ingestion and sifts through the data so you don’t have to.
With Alert Logic MDR Professional you will be assigned your personal MDR Concierge. Their goal is simple: ensure customers are receiving the best possible service by understanding their unique needs and facilitating those within Alert Logic.
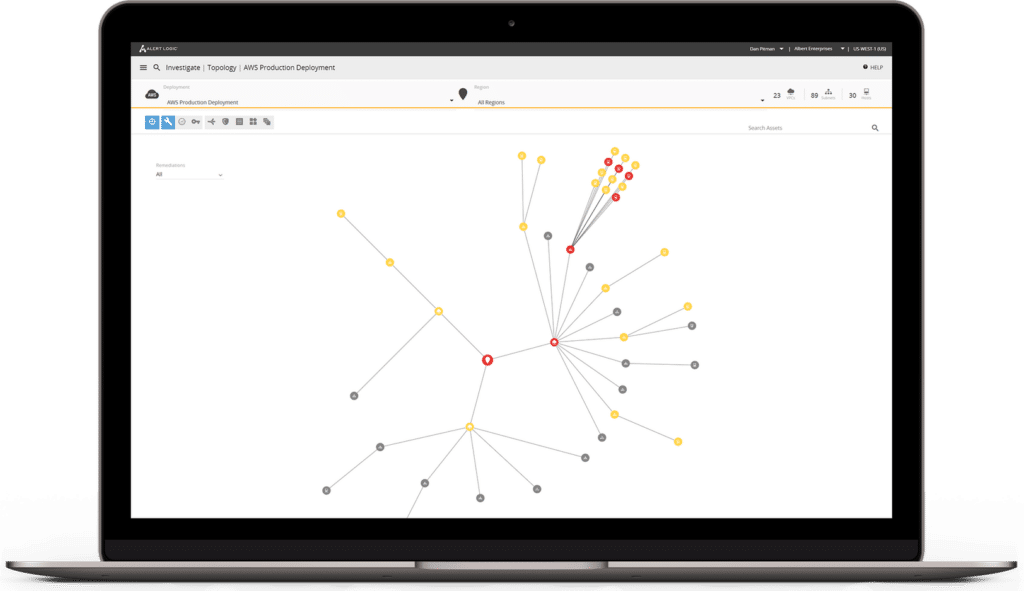
Hybrid Threat and Risk Visibility
Alert Logic MDR Professional provides a complete view of attacks, threats, and risks in all your environments by combining the benefits of Alert Logic MDR Essentials with 24/7 threat detection and the Alert Logic MDR platform.
Continuous vulnerability scanning provides a view of exposure across all your cloud, hybrid, and on-premises systems. Rapidly see relevant information through dashboards, which enable targeted response and analysis of everything affecting your security posture.
Gain in-depth insights into vulnerabilities, attacker behavior, and validated security incidents with just one click.
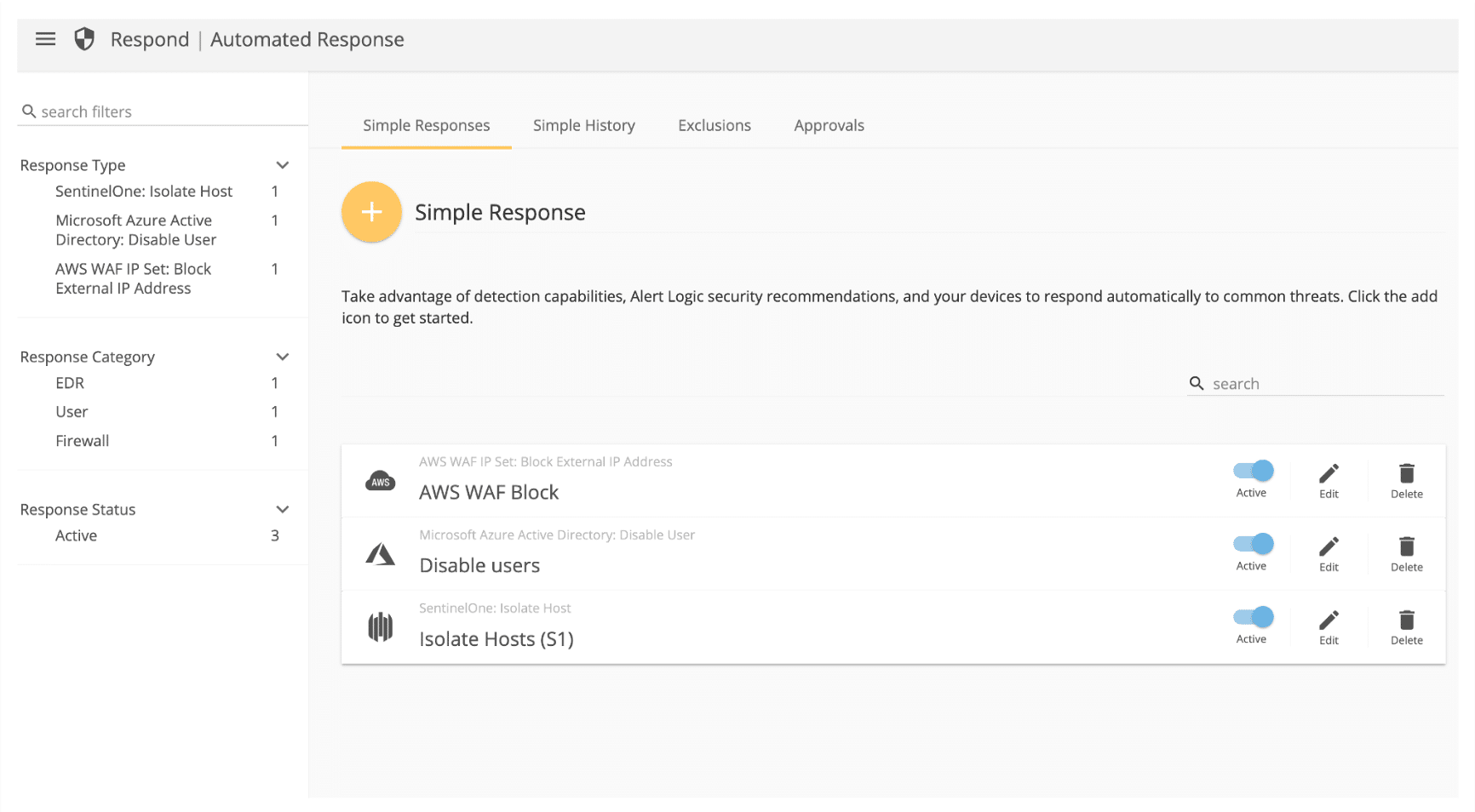
Automated Response (SOAR)
Comprehensive Coverage
Cross-Environment
Managed Cybersecurity Solution
Hybrid Cloud
Alert Logic’s MDR platform supports the flexibility of a combined infrastructure with security and compliance across your hybrid cloud environment.
ON-PREMISES
Alert Logic provides data center security and compliance for any environment – including on-premises infrastructure and applications.
Public cloud
Alert Logic’s MDR solution runs in the leading public cloud platforms: AWS, Microsoft Azure, and Google Cloud.
Additional Capabilities
15-minute
Escalation SLA
Alert Logic analysts have 15 minutes to triage threats raised through hunting or the Alert Logic MDR platform, and determine if the threat requires escalation.
Named MDR Concierge
Comprehensive Compliance
Benefit from a broad range of protective measures and be prepared for audits, anytime. Audit-enabling reporting helps IT staff stay one step ahead of requirements, mandates, and auditors.
Cloud Change Monitoring
Real-time Reporting
Intrusion Detection
Security monitoring and analysis from certified security defenders. Receive expert guidance to quickly respond to attacks against applications, servers, and containers on-premises and in the cloud.
File Integrity Monitoring
Alert Logic detects unauthorized changes to files on Windows and Linux servers. By monitoring for suspicious file change events, organizations can meet regulatory compliance standards.
User Behavior Anomaly Detection
Web Application Threat Detection
Continuously analyzes network and log data, providing visibility into web application attacks, visualizing and reporting on threats and exploits. Innovative machine-learning log data analysis provides attack visibility, regardless of your chosen encryption methods.
Resources
Get to Know
Managed Detection and Response
Compare MDR Subscription Tiers
Each subscription provides different levels of vulnerability and threat management services and capabilities
for your on-premise, public cloud, or hosted data centers.