As part of the Alert Logic technical analysis of these threats we occasionally identify entirely new vulnerabilities or bypass conditions for previous vulnerability patches. During our work on coverage for a reported vulnerability in the MapPress plugin for WordPress, a bypass was discovered in the latest version of the plugin which would enable an attacker with subscriber privileges to download or delete arbitrary PHP files or upload arbitrary malicious PHP files to vulnerable sites, which could result in remote command execution. Following our responsible disclosure policy, we contacted the developer to report the issue and work with them to resolve the underlying issue as well as reported the vulnerability to MITRE (CVE-2020-12675).
MapPress Plugin
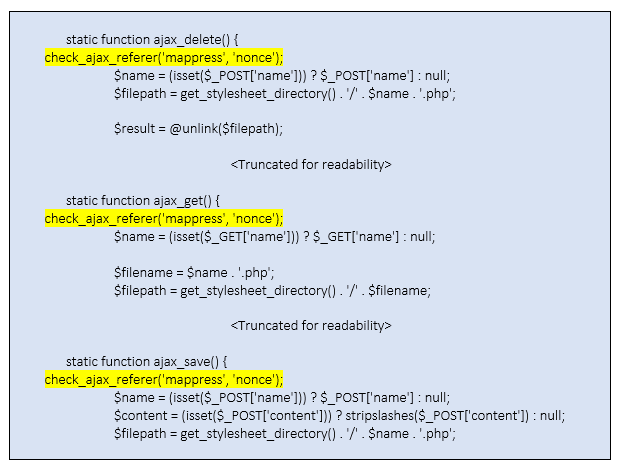
The vulnerable functionality was originally identified in versions prior to 2.53.9 of the plugin as described in CVE-2020-12077. The plugin enables site owners to create custom templates, written in PHP, to control how maps are displayed. The lack of capability or nonce checks identified by the original vulnerability report was considered resolved in version 2.53.9 of the plugin. Unfortunately, the implemented protections for CVE-2020-12077 were not sufficient to resolve the underlying issue and the plugin remained vulnerable. The implemented fix introduced a nonce check, but no capability check, in each of the AJAX functions. The bypass then simply required a valid nonce value to be submitted along with the AJAX call to once again exploit the vulnerable upload functionality.
Technical Analysis
The root cause of the vulnerability is a lack of capability checks, as highlighted in the original report, in what should be restricted functionality. The implementation of a nonce check addresses the potential for cross-site request forgery (CSRF) style attacks against the upload functionality but does little to verify that the requesting user is authorized to utilize said functionality.
As an aside, while reviewing the vulnerability we determined the lack of input validation allowed path traversal characters, which would also allow users with minimal permissions to view or delete arbitrary PHP files. This could provide an alternative avenue for site take over by first leaking the database info from, then deleting, the ‘wp-config.php’ file and putting the site back into installation mode.
Path: /mappress-google-maps-for-wordpress/mappress_template.php [Lines: 35-73]
The above changes prevent blind AJAX upload requests from being made, as a valid nonce must first be sourced and submitted along with the upload. As part of the script localization process, valid nonce values are generated and included as part of a script block on any page that includes MapPress map content. All an attacker needs to do is visit a page on the target site which contains map content and harvest the generated nonce value, again exposing the AJAX functionality to attackers with minimal permissions on the site.
Remediation & Mitigation
The primary resolution of this vulnerability is to update to the latest version of the plugin. If this is not possible, then mitigation options may include:
- Virtual patching using a WAF to filter AJAX requests destined for the vulnerable AJAX functionality (‘mapp_tpl_get’ / ‘mapp_tpl_save’ / ‘mapp_tpl_delete’)
Responsible Disclosure
| What | When |
| Initial contact with Vendor | April 30, 2020 |
| Vulnerability Disclosed to developer | April 30, 2020 |
| Submit to Mitre, CVE assigned | May 6, 2020 |
| Version 2.54.6 released, Confirmed no longer vulnerable | May 6, 2020 |
| Responsible Disclosure embargo lifted | May 27, 2020 |
| Public Disclosure | May 28, 2020 |