Reduce Risk While Accelerating Business Growth within Azure
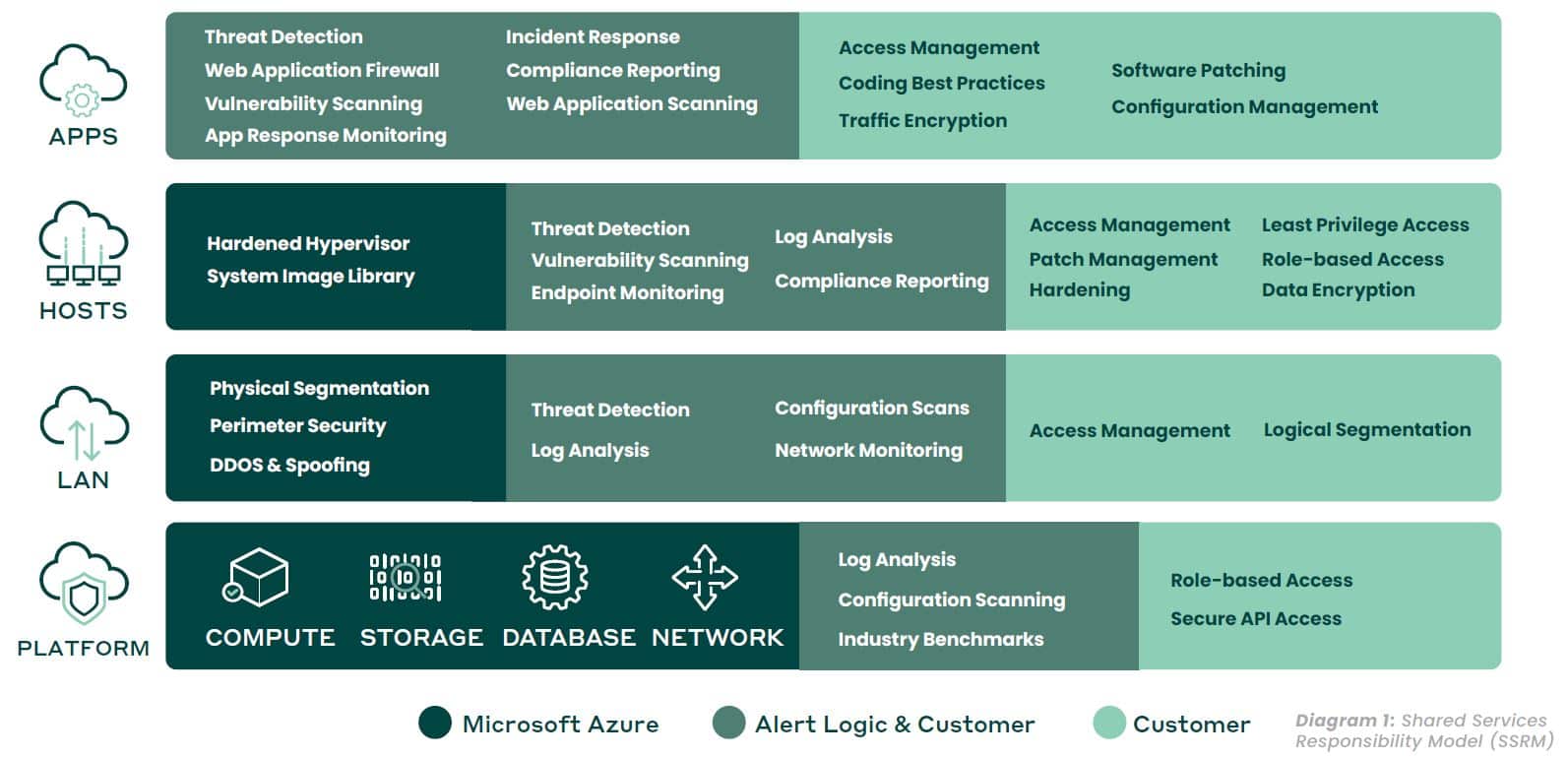
Using public cloud infrastructure-as-a-service (IaaS) for your applications and other workloads creates new flexibility and economy for your business, but organizations struggle to address the rapidly evolving IT security landscape. Protect what you deploy on Azure against cyber threats and attacks while maintaining the elasticity your business needs.
Your Azure environment requires up-to-date security technologies with 24/7 security monitoring to identify and protect your applications and workloads against cyber threats in real time.
That’s why we created a solution built specifically for securing your Azure environment deployments. Alert Logic provides a cloud-native, managed security solution that provides complete security visibility and addresses a broad set of security compliance controls.
Azure Security Monitoring Made Simple
Alert Logic provides an integrated suite of managed infrastructure and workload security and compliance controls for your Azure environment, all delivered to you as a single service. This includes:
- Intrusion detection systems (IDS) can identify various attack methods and security threats within your network traffic. This includes vulnerabilities in web application frameworks, container technologies, application stack components, and attack techniques listed in the OWASP Top 10.
- Log management to meet compliance requirements and identify suspicious behavior from a comprehensive group of sources, including Azure Monitor and Azure Storage Accounts (Blobs or Tables), and Azure-deployed containers
- Vulnerability management and security configuration management to assess your security posture and identify vulnerabilities hidden at all layers of your application stack
- Expert incident analysis and live notifications of critical attacks from one of our expert security analysts
- A broad set of security compliance controls for GDPR, PCI DSS Compliance, HIPAA, and SOC 2 —including PCI ASV attestation reporting and fully managed and centralized logging
- Azure Event Hubs integration with machine-learning analytics for behavior and anomaly detection
How We Do It
Designed for Microsoft Azure
Alert Logic has built its security solution for applications and workloads on Azure with agility and scalability in mind. Our microservices architecture and RESTful API are designed to integrate seamlessly with Azure’s native tools, including Azure Monitor and Azure Storage Accounts. This enables our platform to embed security directly into your CI/CD pipeline and dynamic production environments.
Simplify Azure Event Hub Monitoring
Quickly find unauthorized activity from the Azure Event Hubs without having to hire internal security experts to investigate alerts, remove noise, analyze and prioritize incidents.
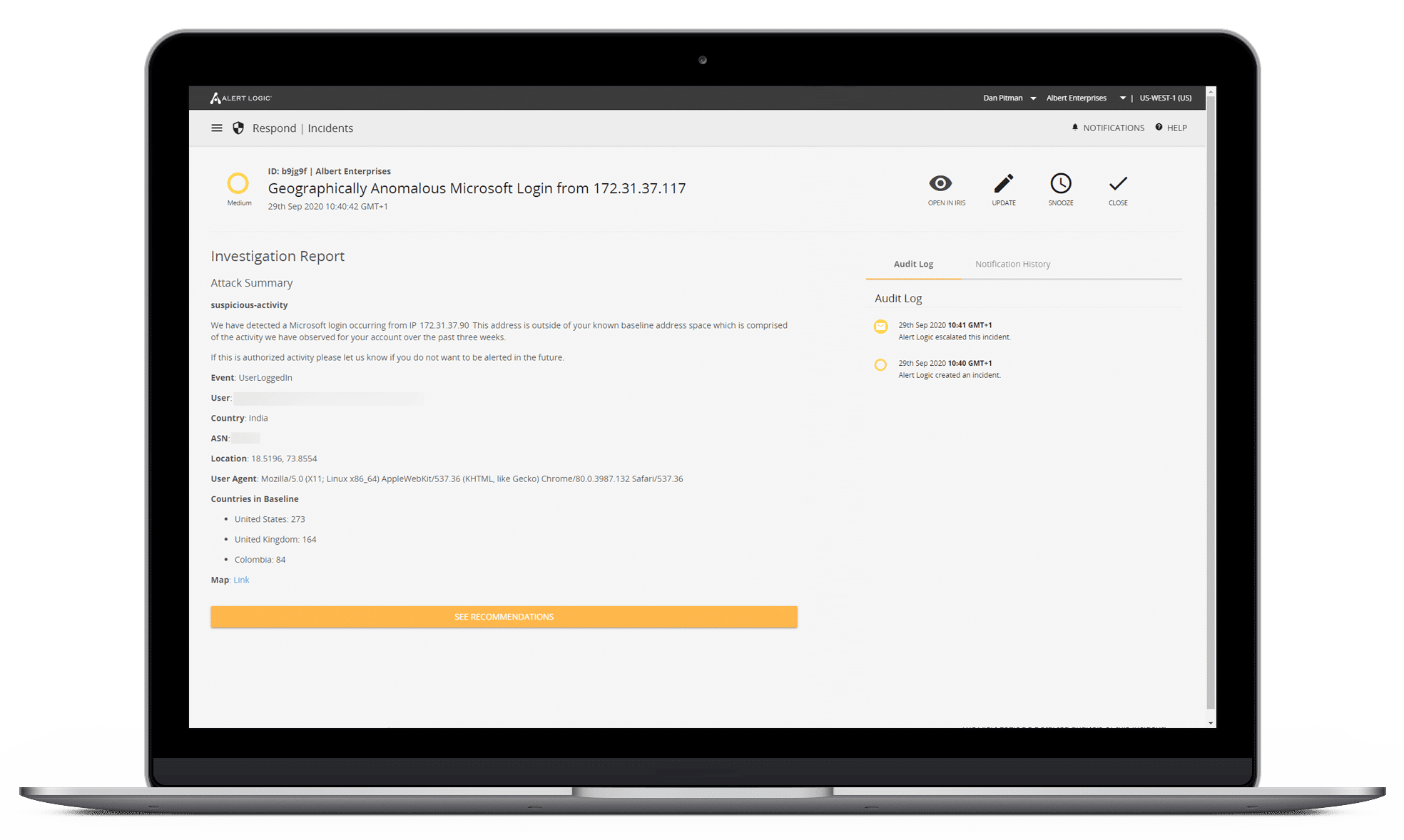
Actionable Threat Detection & Response
Security data is collected, aggregated, and analyzed to detect attacks. High-priority threats are confirmed, and you are promptly notified with remediation recommendations to address the incident.
Experts Monitoring Your Environment
Our team of security experts identify, review, investigate and escalate incidents to proactively protect against cyber threats 24/7.
Enhancing Web Application Security
With Azure Event Hubs integration, we add additional security context to web application security, network vulnerability scanning, log correlation and reporting.
Benefits of Azure Security with Alert Logic
Alert Logic provides agile security services that scale with native API-driven automation and templates for Azure and DevOps tool chains, delivered as a single subscription. This allows you to:
- Focus on the most cloud-relevant threats with full-stack protection of your full application and infrastructure stack
- Accelerate production with API-driven automation and elasticity
- Add cyber security experts to your team overnight without hiring staff
- Preserve application performance with lightweight agents and auto-scaling support
- Simplify with one service that works across all your Azure, on-premises, and hybrid environments.
Capabilities
Threat Management
Seamless integration of platform, threat intelligence, and expert services
Cybersecurity Monitoring
We offer a comprehensive platform, backed by real-time threat intelligence and a team of expert defenders, providing 24/7 monitoring to protect your business from attacks, threats, and potential risks
Web Application Firewall (WAF)
Fortra Managed WAF is your frontline defense against attacks. Deployment models match your requirements and offer 24/7 monitoring for solid protection against compromises.
Network Intrusion Detection System (IDS)
Our IDS and vulnerability assessment services monitor your network, identify suspicious activity, and provide verified alerts and recommended remediation steps.
Vulnerability Scanning & Assessment
Log Management
Our log management solution collects and normalizes your log data, while our 24/7 expert monitoring and analysis adds human intelligence to find key insights.