When I was a child, my father was a huge superhero fan. He used to tell me all about Superman and Batman and all the intricacies of the character’s back stories and personalities. This made it very easy to dive right into the movies and comics containing the characters and know exactly what was going on and what to pay attention to. As I got older, I started to broaden my horizons and gain interest in other superhero characters. But, without my father’s helpful contexts, I had to go back and read a lot of the superhero origin stories and play catch-up to jump into the newer material. This became an almost overwhelming task!
I find cybersecurity is very similar regarding having to do a lot of investigation and research. There’s usually a limited staff of security experts and only so much time in the day. One big difference is it becomes paramount to find and react quickly to cybersecurity issues. This means not only just being right a lot, but also being right expediently.
Too Many Alerts, Too Few Cybersecurity Experts
A recent study found some organizations are running too many separate security tools. This can overwhelm thinly stretched security staff with too many alerts from multiple tools who are constantly playing catch-up to verify and prioritize incidents. When there is a limited number of security experts, this can cause an even longer delay of trying to appropriately identify a security risk/threat quickly. A typical scenario like this can cause a delay of 200 or more days to find a security breach. As one can imagine, this means that the bad guys are already in and possibly extracting valuable data.
According to a recent State of Cybersecurity study from ISACA, 69% of respondents say their security teams are understaffed. This causes the often-asked question of “Okay, now what?” when there is an attack detected or suspected. That translates into the unique task of what to have stretched resources focus on to provide an effective cybersecurity approach. If the security staff is occupied on something that isn’t a high priority, it can leave a huge security hole open and a possible breach that could go undetected for days or months.
Simplify and Streamline Cybersecurity
Limited resources dealing with alert fatigue and multiple tools should raise the questions, like ”Can’t we just have a unified tool and approach to security?,” or “There must be some way to have these alerts consolidated and curated before we look at them,” or “How can we prioritize the findings effectively?”
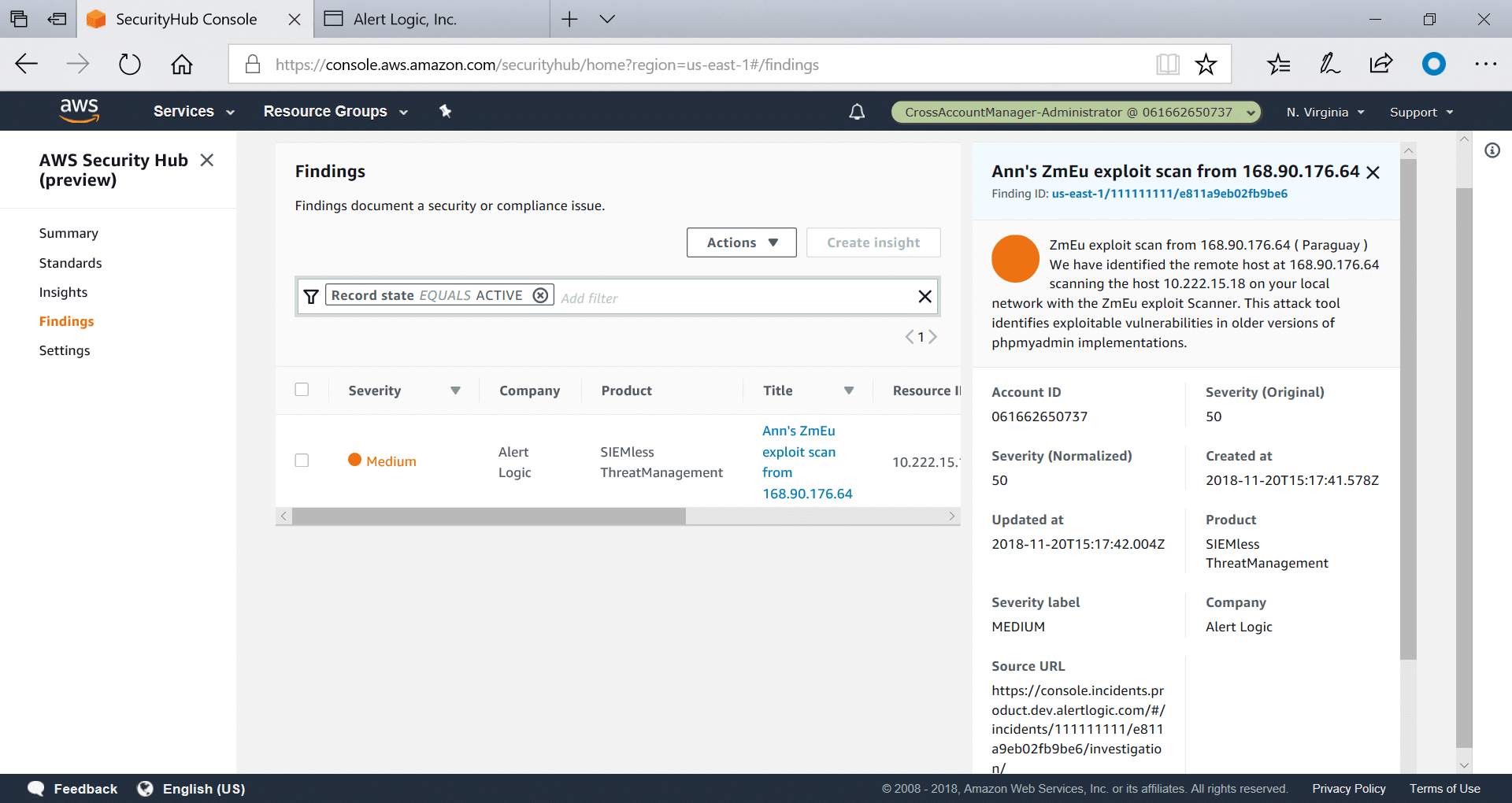
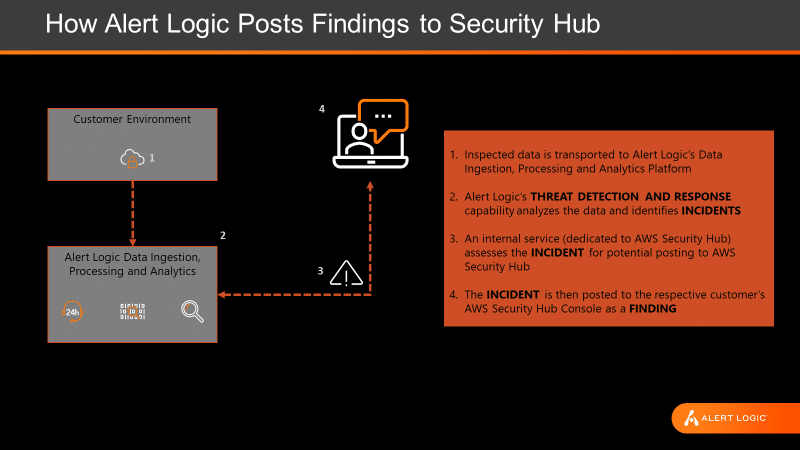
AWS Security Hub can provide this centralized approach and provide one place for correlated and verified alerts that can be prioritized. Alert Logic has a seamless integration with AWS Security Hub. This allows for curated intrusion detection events to be pushed into your AWS Security Hub service via API. These events give detailed information on the finding and provide a link that goes into even further detail, such as packet reconstruction. If you have an Alert Logic account, you can simply go into Security Hub, click on “Search for Providers,” search for Alert Logic and click the enable button. If you don’t have an Alert Logic account, you can go to the AWS Marketplace and sign up for an account there and then follow the same steps to enable Alert Logic – AWS Security Hub integration.
This also provides an opportunity to further automate by utilizing AWS Cloudwatch events as a trigger for automated remediation.
As a result, you will get correlated and verified incidents—prioritized so your team can take action. This will also result in both a better security posture as well as higher performance from the security team as they don’t have to validate or hunt for incidents and have a list of prioritized items to address.
Learn more about Alert Logic and AWS security.
Additional Resources:
AWS Security Simplified: Support for the Shared Responsibility Model
Schedule an Alert Logic demo to see for yourself how we protect AWS workloads