Looking back on 2017, there’s no doubt that its an exciting time to be working in the cloud space and cloud security. The speed and depth of innovation was—and continues to be—simply staggering. We could just as easily make the case to say that 2017 was the year of serverless technology…or machine learning …or stream processing …or name just about any other cloud microservices and it likely saw at least double-digit growth in 2017. Point being, it’s only the beginning, so get ready for 2018 to continue the breakneck evolution of cloud technologies.
Cloud security breaches are keeping pace with cloud innovation by becoming increasingly dynamic, utilizing multi-pronged approaches, capitalizing on inherent vulnerabilities, or lying dormant until the next opportunity to exploit cloud vulnerabilities at any layer of your software stack—so make sure you’re prepared to defend the full stack.
[Related Reading: What is Cloud Security?]
Rapid Evolution of Cloud Security
In 2017, AWS alone released over 1,300 new capabilities. Voice controlled smart home systems such as Google Home, Amazon Echo, and companion devices have ignited tremendous growth in natural language processing and IoT to the tune of some 27 million households. Businesses of all types and sizes continue to invest in the IoT space in order to manage fleets, track shipments, collect telematics data, and build out new competitive capabilities—giving life to an estimated 8.4 billion internet-connected endpoints.
As cloud technology continues to evolve and grow more sophisticated, so does the threat landscape and challenges of application security. In 2017, we saw highly publicized cloud data leaks at major public and private organizations such as Verizon, Uber, the NSA, Equifax, and most recently at Alertyx. We also saw WannaCry ransomware wreak havoc in one the largest cyber-attacks in history, an attack the US officially blamed on North Korea. These types of security threats are very real in today’s world. Couple that fact with the speed of innovation and scale and complexity of modern cloud architectures, the scope of the ever-growing attack surface is becoming an increasingly challenging feat.
Defending the Full Stack
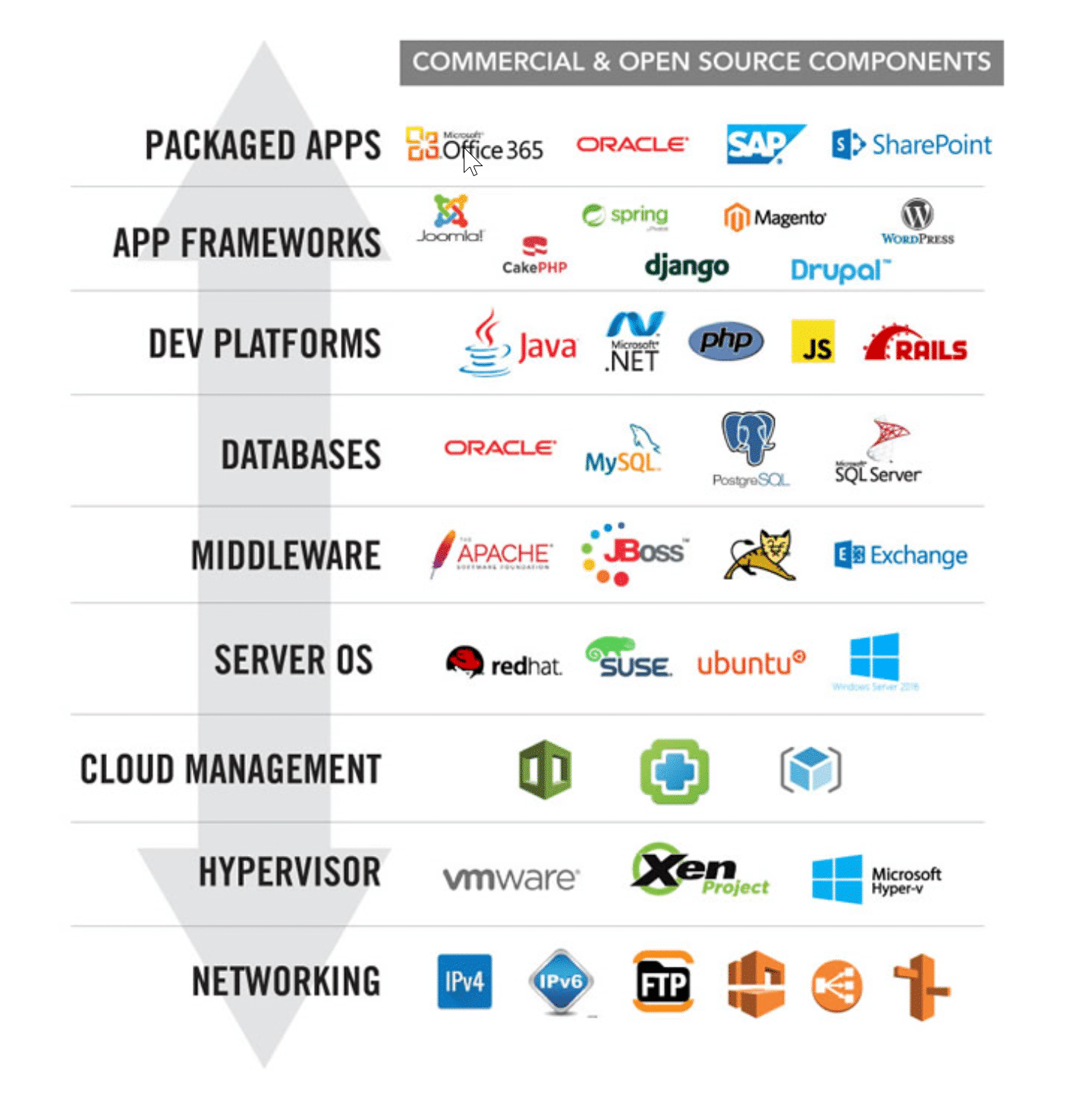
Alert Logic’s 2017 Cloud Security Report outlined an increasing trend in cyber-attacks in which criminals were stringing together chains of vulnerabilities in order to build hard-to-detect attacks. These attacks targeted primarily web applications—which our research has proven to be the primary method by which attackers breach data. Consider that most modern web applications running in the cloud are built on an application stack comprised of the following nine components:
The lower levels are generally handled by your cloud service provider (CSP)—think AWS Shared Responsibility Model. That being said, don’t assume that your CSP will take care of securing the Infrastructure-as-a-Service (IaaS) components that you deploy. CSPs secure the cloud infrastructure itself. You, as the customer, are responsible for the security and management of those low-level resources and how you use them.
Having trouble pulling all this together? The bottom line is that securing web applications in the cloud is becoming increasingly complex. Alert Logic employs a full stack approach to application security, providing ongoing protection against vulnerabilities in your code and configurations from the network layer all the way up to your packaged apps. In the coming weeks, we’ll be unpacking our full stack security approach in a blog series with specific use cases, examples and customer stories. We’ll also be walking through some of our new capabilities and demonstrate how Alert Logic’s security platform can help you assess, detect, block, and effectively defend against threats while also supporting regulatory compliance requirements using our full stack security approach.
Next post in our Full Stack Security series focuses on protecting packaged applications.
Check out the complete series on full stack security: