Securing your containers is critical
Container adoption is skyrocketing, growing year on year. But security is increasingly a major concern and the top roadblock to container deployment.
The security industry has responded with process monitoring, vulnerability management, and configuration management. These are great steps, but security teams continue to struggle without the ability to inspect the network traffic that targets containers. This enables suspicious activity within your container environments to go undetected and leaves you susceptible to a container or base host compromise.
With Alert Logic:
- Receive proactive notification from our security experts when suspicious activity is detected in your containers
- Build a better view of security impact with a graphical representation of the compromised container and its relationships
- Easily collect, aggregate, and search container log data to support compliance regulations
- Deploy our native container monitoring solution easily using industry standard methods
- Leverage one integrated security solution to protect all your workloads – whether in a container or not
Request My Demo
Key features and benefits
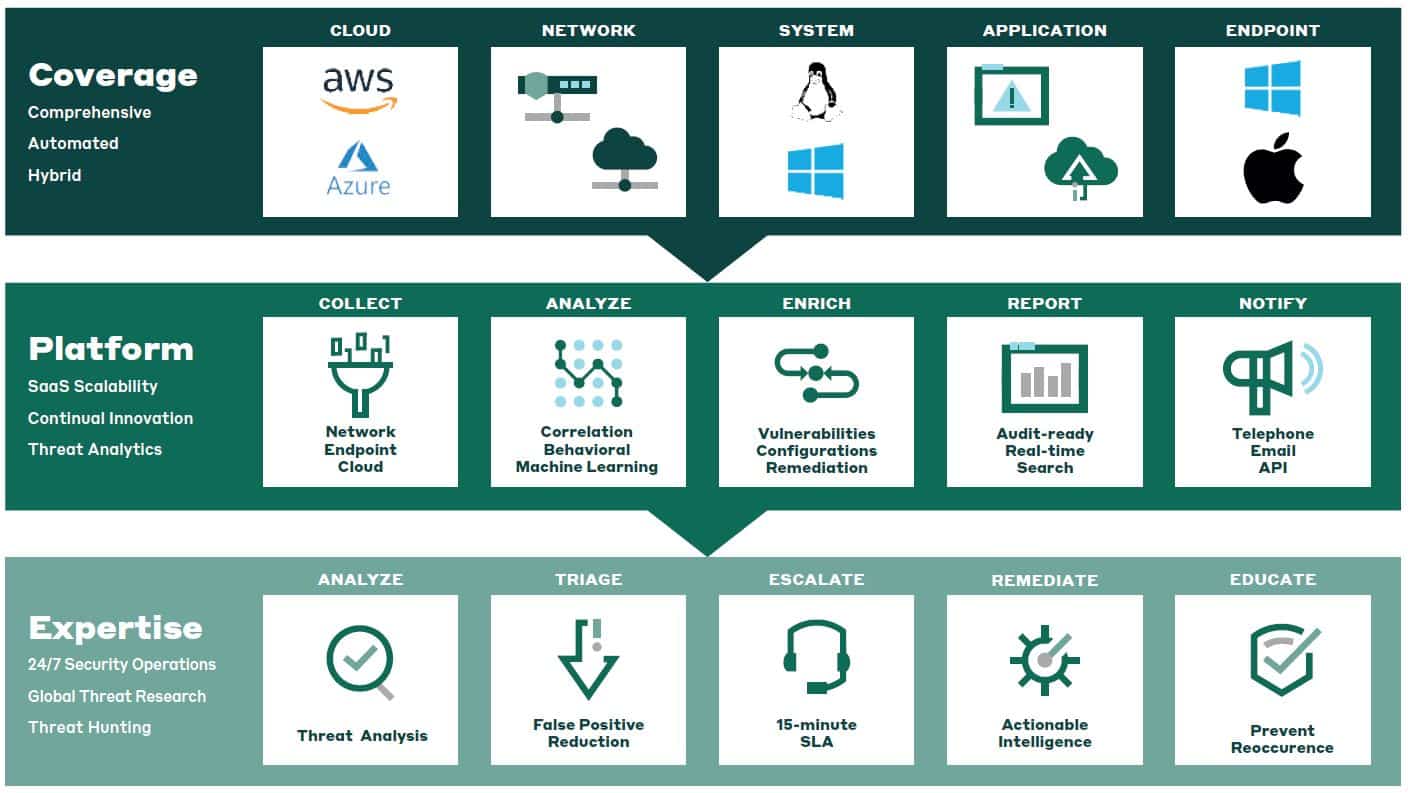
Comprehensive container security
at the network level
Alert Logic provides a complete view of your container environment by collecting and analyzing network traffic from the base host and the network traffic to, from, and between containers. This comprehensive approach provides better visibility, consistency of management across multiple platforms and portability–ensuring that you can manage your containers across platforms, in hybrid environments, and on-premises.
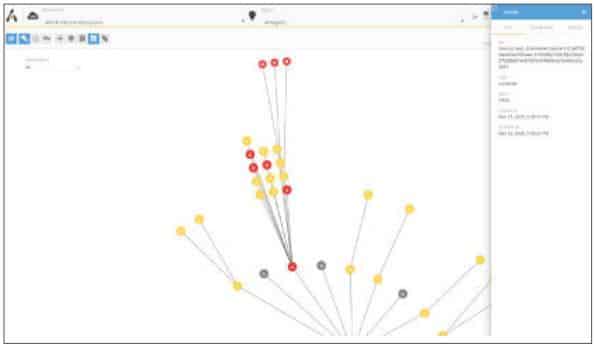
Quickly explore container incidents
The Alert Logic Incident Console makes it easy and intuitive to understand container incidents. Visualize which containers and hosts may be compromised, examine the associated metadata, and explore remediation recommendations. You can also integrate with the Alert Logic Incident API to support your existing security policies and workflow. With a consistent log interface, you can manage all of your containers in one, simple-to-use console regardless of platform.

Easily collect, aggregate, and search
container log data
Log management is an important infrastructure management best practice, and is an essential component of numerous compliance regulations. Containers are no exception. Simplify your container environment by leveraging the same container to collects logs AND analyze network traffic.
Protect AWS, AZURE, Google Cloud platforms, and on premises hosted containers
Protect against cyberattacks that target your containers with a solution designed for real-time detection of known and unknown exploits for Docker, Kubernetes, Elastic Beanstalk, CoreOS, Amazon Elastic Container Services (ECS & EKS) and AWS Fargate.
Alert Logic experts are there to help you every step of the way
When a container threat is detected, we prioritize it, proactively escalate it to you within 15-minutes, provide visual context, and offer remediation advice – so you’re never on your own.
Leverage one security solution across multiple environments
If you’re like most organizations, your environment is a mix of on-premises and one or multiple cloud providers. With Alert Logic, you can leverage one integrated security solution to protect all your workloads – whether in a container or not.
Simple, Self-service delivery
Getting up and running is easy – it’s a container! Just use the same self-service practices you have in place for the rest of your container environment.

Secrets To A Stronger Strategy For Container Security
Learn how you can develop a stronger container strategy for securing AWS container deployments.





